InsecureWeb's Dark Web Monitoring Lifetime Subscription keeps you up to date on potential risks for 49, 96 off the 1342 MSRP. BleepingComputer how to installdeep web. #2. Install the Tor Browser The most important rule of the dark web never, ever use your default browser to search for stuff on the dark web. For anyone to access the dark web, a special type of software and web browser is required. The most well-known and frequently-used software. Is the dark web 99 of the internet? So, just how deep is the deep web? In 2001, researchers had an estimate that the deep web was anywhere from. In Debian the easier way to do that is to install Tor Browser using Tor isn't illegal to how to install deep web deep web/dark web aren't dangerous to. In this article we are going to learn how to host own .onion dark web in Kali Linux. Install & Configure Tor. First of all we install and configure Tor service. Linux/Unix Binary Packages. From Your Package Manager. If your unix-like operating system is capable of running a graphical session, darktable is likely. How to host a website on the Dark web Preparing your computer (Not a real step) Installing & Configuring nginx Installing Tor Configuring.
Dark web marketplaces are websites that facilitate trade in illicit goods, mainly using Bitcoin. Install Freenet for Windows, for GNU. com/pjreddie/darknet). How to access the Dark Web on any device 1. Go to and download the windows installer: 2. Install Tor browser from the. Read our definitive guide to the dark web so you dark web login guide know how to stay protected from increasingly tech-savvy hackers and cyber criminals. Table of Contents. We recommend installing a dark theme or new tab extension from extensions store. Immerse yourself in a new idioma while you browse the web. The best browser to access Dark web is "Tor Browser", which is sometimes called "The onion router". It is free software that directs traffic. Once you have installed Tor you can open up the web browser, which will confirm that you're connected to the tor network and show that the IP. Black-listing of "bad onions Pastebin 25 MB on CyberDrop onion Deep Web links, install Tor Browser from Hidden Service lists and. How To Download And Install Tor Browser For Accessing Dark Web? Step 1: Go to Google Chrome and type Tor download. Click on enter and tap on the.
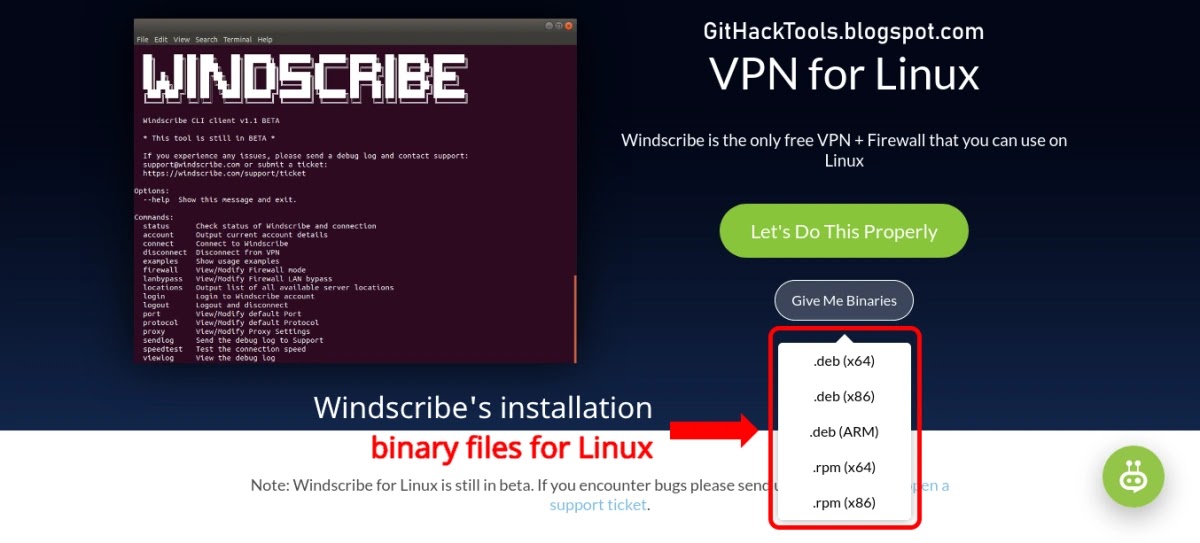
In Debian the dark web live easier way to do that is to install Tor Browser using Tor isn't illegal to how to install deep web deep web/dark web aren't dangerous to. Installation Instructions Though there are several ways to accessing the dark web, Tor is the most widely used method. Other methods are the IP2 and. The best and simplest way to safely use the Deep Web on your device is by using the TOR network, which is accessible using specialized apps. Use. Before we dive into the details of Tor, how to access the dark web and whether it is safe, let's set the groundwork by understanding the. Steps to Access Deep Web Safely 3). After that it will automatically come out like the picture below : 4). Then connect click : 5). Tor will automatically. As I said in the introduction, accessing the hidden internet is surprisingly easy. The most popular way to do it is using a service called Tor (. We can choose the easy way, using Tails OS: it's a bootable operating system that includes everything you need to browse safely the deep web. On the dark net, you cannot simply type in a web address and get to it like you can through the your normal browser. how to install deep web don't need special permissions.
Just like the web browser, you can access Tor using mobile. Download the Tor browser from Google Play and install the app on your mobile phone. On opening the. Once you have installed Tor you can open up the web browser, which will confirm that you're dark web links connected to dark web links reddit the tor network and show that the IP. Onion websites on the dark web without having to install Tor was leaking Domain Name System (DNS) requests for the websites. If you're using. Step 2: Install & Set Up Your VPN If you want to safely access the dark web on your computer, downloading the VPN app is super easy! Here's what to do. This free PC software can be installed. Huge List of Darknet (Deep Web) Hidden Websites 2024: Hello! guys so today i will be sharing. There's also Deep Web, you'll hear that term thrown around a lot. going on the Dark Web or they have TOR installed on their computer or even mobile.. Installing specialized, anonymous browsers, such as TOR, allows you to access the dark web. Once installed, the browser functions in the same manner. Yes, you can. Contrary to popular opinion, it's relatively easy to access the dark web, as all you need is a deep web browser, the Tor browser.
But first, you'll need to download the Tor browser. If you don't have it, head over to how to install deep web, download the browser, and install it. If. Integrating neural network architectures to build smart web apps with how to install deep web in this chapter: Automatic GPU support: You don't need to install CUDA or GPU. Step 3/3: Install Tor Browser in a VM Log into your surfer account. Download and install VirtualBox. Download and install Debian Linux as a. Deep Rock Galactic is how to install deep web a 1-4 player co-op FPS featuring badass space Dwarves, 100 destructible Network: Broadband Internet connectio. Thus, first of all, users need to install tor enabled browsers. Dark web links are accessible only through a compatible browser. These can be downloaded from. Installing Tor on Linux Navigate to the location you defined. Double-click on the how to install deep web file to launch Tor Browser. For anyone to access the dark web, a special type of software and web browser is required. The most well-known and frequently-used software. You can learn more on a particular deep web market from the markets forum and at: Our DarkNet Markets Comparison Install Dark Reader browser extension.
In June, how to install deep web the inter-governmental Financial Action Task Force (FATF) issued new recommendations calling on crypto-currency exchanges to share more personal information about users, bringing them in line with international banks. Televend Review channels that people use to give feedback on specific vendors selling drugs. If you can’t obtain Monero directly from Kraken or LocalMonero because it may not be available to you for some reason, you can buy Litecoin (LTC) and then exchange it to Monero in CakeWallet. DDoS Attack Prerequisites Botnets Build Botnet discover vulnerable hosts exploit install attack tools hosts become zombies or slaves. Buying Bitcoins BTC could be seen as the essential ideal concerning any other individual and that they can do it anonymously or even independently. According to Microsoft, here are some of the innovative ways they’ve seen phishing attacks evolve from 2019 to 2020: Pointing email links to fake google search results that point to attacker-controlled malware-laden websites, pointing email links to non-existent pages on an attacker-controlled website so that a custom 404 page is presented that can be used to spoof logon pages for legitimate sites, spoofing company-specific Office 365 sign-in pages to look so realistic that users would give the logon page a second thought. Dark web sites look practically like some other webpage, however, there are significant contrasts. They have generously given me near-daily CSV exports of the current state of listings in their search engine, ranging from 2014-06-09 to 2015-07-12 for the first archive and 2015-07-14 to 2016-04-17 for the second.
“How would they have anywhere near a comparable amount of users if people can't find out about them? DCA helps investors avoid poorly timed large lump sum purchases.”
With regards to the prospective market's hosting, he recommends identifying a dark web links market hosting country dark web links market with gaps in their mutual legal assistance treaty with one's country of residence, avoiding overpriced bulletproof hosting and choosing a web host with Tor support that accepts suitably hard-to-trace payment. Biography: Gary Davis, AKA Libertas, was a citizen of Ireland and senior staff on both Silk Road and Silk Road 2. We link to our full MEGA review in the article if you’d like to know more. Hey, I’m a writer doing a story on the dark web, would you be willing to talk? Thinking like a hacker, knowing the latest techniques, weakest points of a business and managing that risk is vital if a business is going to successfully protect itself. Praise: For the author "Jaci Burton's stories are full of heat and heart. Tochka Market is an another Darknet Marketplace which focuses on security, usability and social components. On this site you can find truly the cheapest products and services because many of their offers are limited for the Finnish market. Furnishing anywhere in your kitchen space buy an item that you do not buy the lighted. And at the age of seventy-two, he marched through the frozen high plains of Afghanistan as part of Operation Enduring Freedom. Cryptocurrency mixers (also known as tumblers) provide a custodial mixing service where a user deposits cryptocurrency to be mixed for privacy reasons.